The Cyberint Research Team work round the clock to unearth the latest threats to SMBs and enterprises. They are on top of the latest TTPs and monitor rising threat groups, malwares and trends.
In the recent weeks, Cyberint has detected a rise in the dark web trade of ‘fullz’, for use in the fraudulent application of disaster loans. This report will focus on a case example affecting the US Small Business Administration (SBA), which is operating a Targeted Economic Injury Disaster Loan (EIDL) Advance program designed to assist small business owners with up to $10,000 in grants.

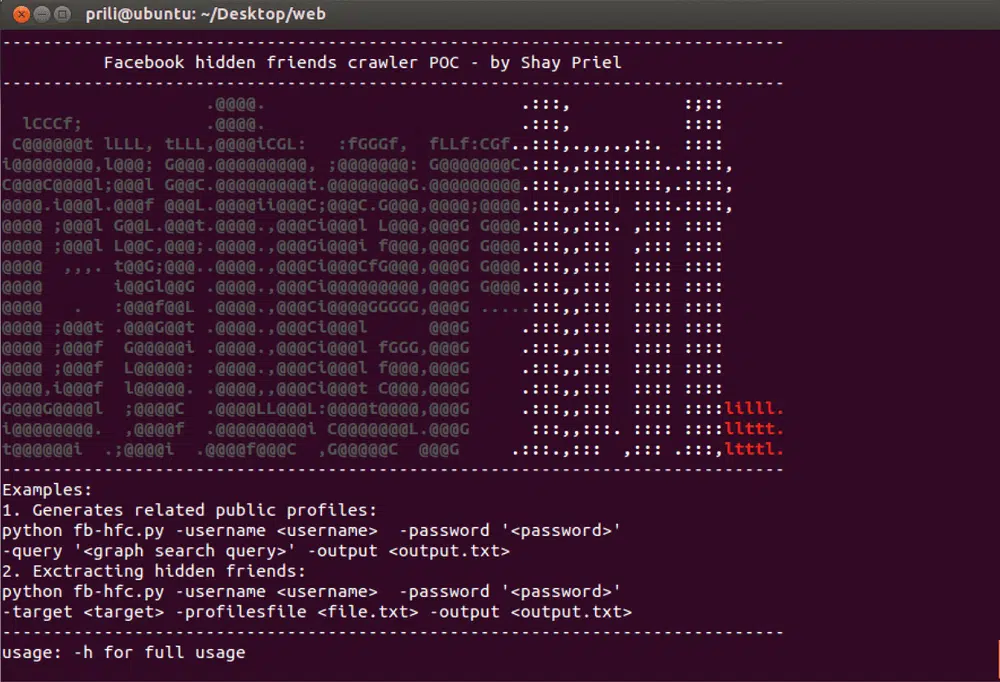
Figure 1 Cyberint’s detection of fullz posted on a deep web fraud forum
‘Fullz’ is Internet slang for “full information”, a term used in the carding and financial fraud dark web markets to pertain to a comprehensive data set of personally identifiable information usually retrieved from phishing operations, web skimming activities on eCommerce platforms, infected endpoint devices with malware, and botnets.
Typically, fullz are most valuable on dark web markets, and useful to threat actors, when they include payment information and logs (See Figure 1). They are commonly utilized to cash out money from the victims’ accounts, as the complete PII in possession of the threat actor can be exploited to bypass online banking verification processes.
For this reason, fullz are typically sold by vendors along with ‘logs’, a term for login information and/or web activities history (See Figure 2), and card cloning services (See Figure 3).
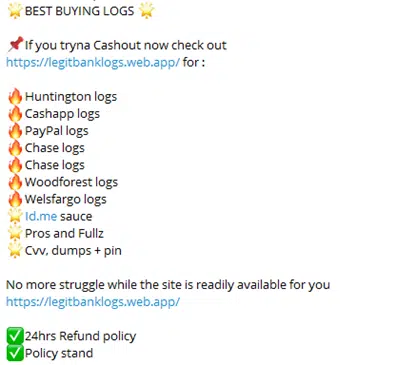
Figure 2 A screenshot depicting how fullz are sold on dark web chatrooms
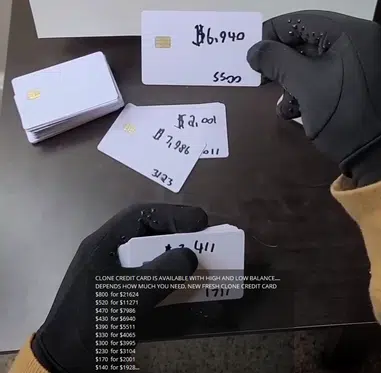
Figure 3 Card cloning services as advertised on dark web chatrooms
In the recent weeks, however, Cyberint has detected threat actors using fullz to apply for fraudulent grants. No payment information needed.
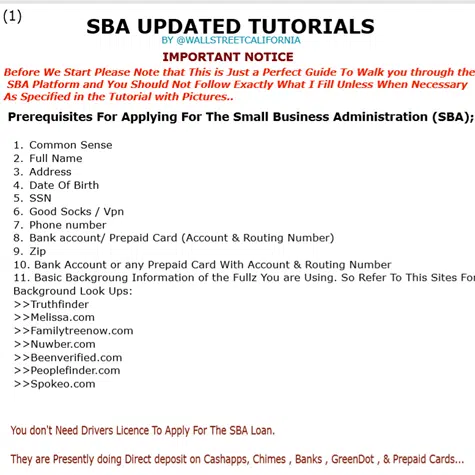
Figure 4 An excerpt of the SBA loan fraud tutorial detected by Cyberint
Various threat actors online are providing complete tutorials on how to exploit the SBA program using fullz:
This is possible because the SBA program is currently doing direct deposit on prepaid cards, online wallets, and cash apps.
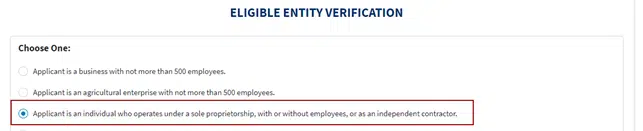
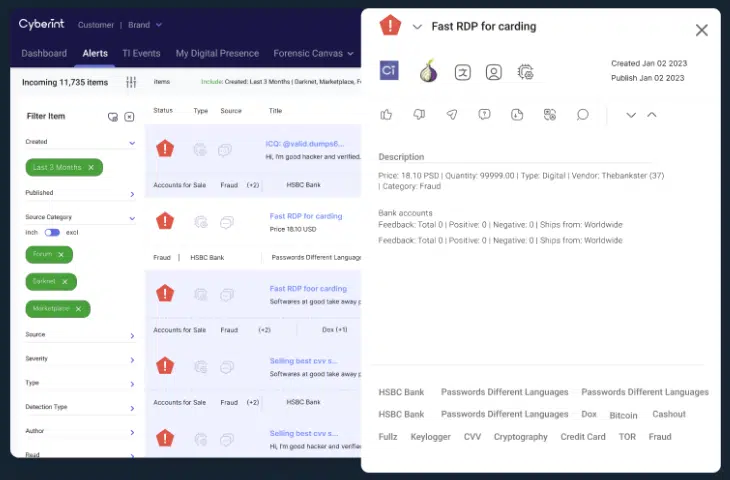
Figure 5 Threat actors advise to apply as sole proprietor for higher chances of success
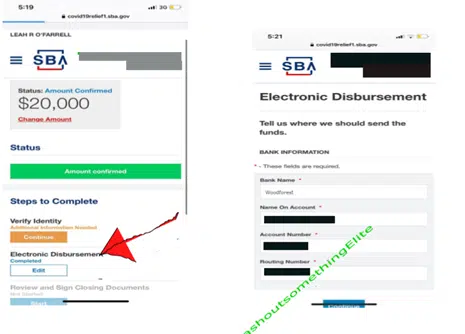
Figure 6 The SBA account appears to allow threat actors to enter drop accounts for the electronic disbursement of the grant
©1994–2026 Check Point Software Technologies Ltd. All rights reserved.
Copyright | Privacy Policy | Cookie Settings | Get the Latest News
Fill in your business email to start