


SMS-based phishing attacks are nothing new. They’ve been around in one form or another since the technology became mainstream in the mid-90s, and more so since the introduction of smartphones a decade and a half ago. However, in their latest incarnation, AKA Smishing, such attacks are progressively executed on a scale never seen before.
In the last couple of months, Cyberint has seen an increase of SMS phishing attacks targeting the customers of retail companies. The recent trend is notable both in its scale and its sophistication.
Previously, Smishing attacks were predominantly used similarly to email phishing attacks, impersonating known personal or business contacts to extract credentials and other victim details. But with the shift to work-from-home, along with the growing use of mobile devices for work and personal use, threat actors are focusing on creating more convincing phishing messages.
One of the most notable recent campaigns took advantage of the massive increase in online shopping by impersonating retailers and shipping companies, in the guise of online purchase package delivery. To add a sense of urgency, the messages often claim that there is some sort of fee to be paid in order to receive the package, and failing to reply will result in the package being sent back to the retailer.
Note that this type of scam is global and is conducted in numerous countries and languages including Russian, Spanish, Japanese and Arabic.
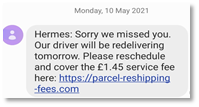
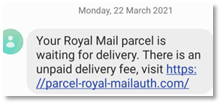
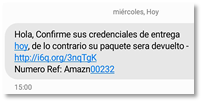
In essence, threat actors in this campaign are leveraging retailer brand names to add a level of authenticity while exploiting the customer’s lack of knowledge regarding the retailer’s chain-of-delivery. This can lead to leakage of credentials, payment info and/or PII, either through redirection to a phishing site or through credential-grabbing malware infecting the mobile device. This in turn may result in customer churn and, potentially, legal claims against the company.
As retail customers receive deliveries on a routinely basis, sometimes daily, many have started seeing notifications regarding package deliveries as “white noise” and as such have lowered their guard. This is exactly what threat actors are counting on. For example, in one campaign, targeted consumers received SMS messages claiming that they owed a customs fee required to release a delivery.[1]
Most messages observed in the recent campaign directed customers to fake websites that request personal and payment info. Concurrently, they also prompted them to update their Chrome app, which downloads malware. Once installed it silently sends 2,000 SMS messages per week from infected devices, without users being aware of it. The messages contain similar phishing content, thus perpetuating and expanding the campaign severalfold.
To obfuscate their activities, the threat actors use multiple techniques. Of note, if the malicious app is detected by an antivirus, the threat actors repackaged the file with a new signature.[2]
Spoofing SMSs on a large scale is also becoming easier and cheaper. SMS bots are widely distributed on file and code sharing sites, and numerous threat actors offer the service on cybercrime forums, as seen below (note: translated from Russian). In many cases the bots operate on networks of infected devices.
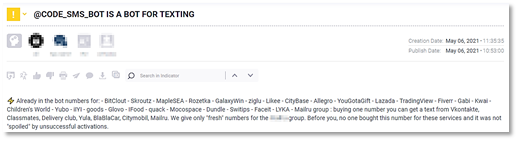
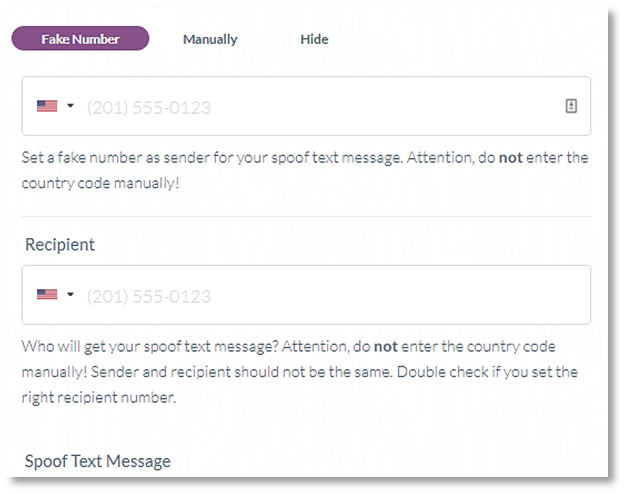
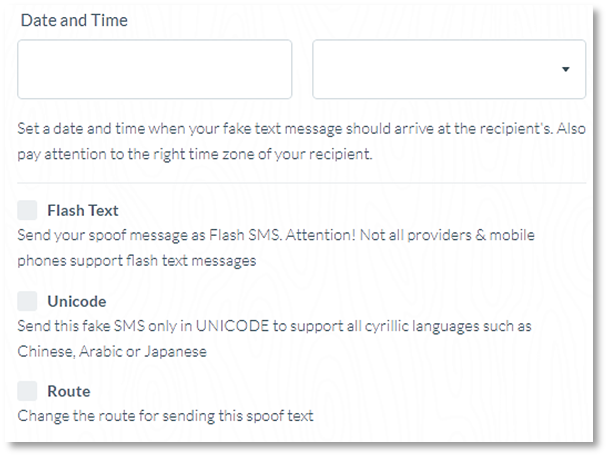
But if this seems too cumbersome or risky, a quick Google search returns dozens of SMS-spoofing services allowing threat actors to operate anonymously and without requiring any technical know-how.
At this point, phishing has become a persistent attack vector in the current threat landscape. While the basic concept remains the same, we are seeing threat actors constantly and skillfully adapting to both new security solutions and global events.
Accordingly, they are putting more effort into low risk, high yield attacks such as Smishing campaigns targeting retail customers. Further, as the shift to online retail continues, and access to attack tools become easier, it is inevitable that we will see more campaigns like these.
As is the case with many types of cybercrime, an affective technology-based solution often comes with a significant impact on both users and companies, and thus may not be a viable option. This is especially the case with Smishing attacks due to the ubiquitous use of SMSs in our daily life.
Accordingly, for the time being, the best mitigation approach to this problem is educating customers about the chain-of-delivery your company employs. For example, it is advised that the email the customer receives upon purchase includes details regarding your shipping policies and partners, as well as the various key red flags your customers should be alerted to. This information could appear in the Q&A section on your website as well. In addition, you should encourage your customers to immediately report any suspicious activity to you, even if it may delay a delivery.
[1] https://news.softpedia.com/news/new-smishing-trojan-impersonating-google-chrome-app-532883.shtml
[2] https://blog.pradeo.com/fake-chrome-mobile-app-smishing-trojan
Fill in your business email to start

