Fraud
Mitigate and Prevent Fraud to Reduce Financial Loss
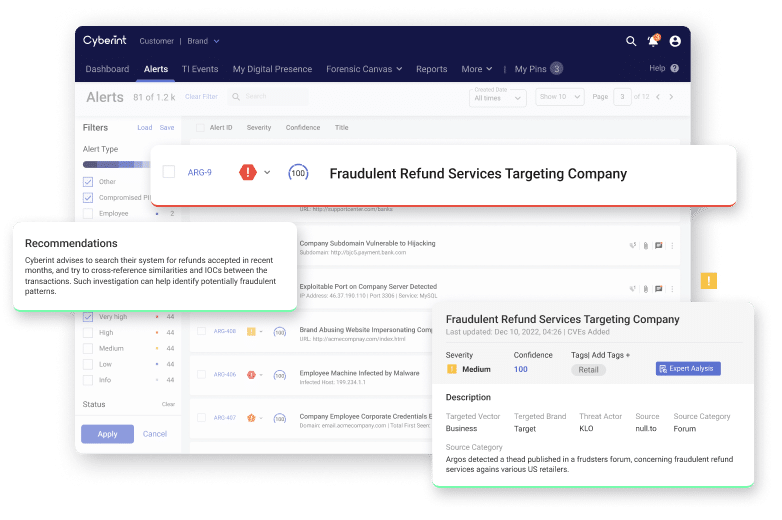
With Argos, your organization can intercept communications between cybercriminals and get information about these continuously evolving fraud techniques and attempts, to thwart these attacks before they even occur.
Detection of phishing URLs
Avg. takedowns/month
IP addresses continuously scanned
Takedown success
We Defend Against All Types of Attacks
Refund Fraud

Carding

Malicious Insider

Money Laundering
Victim Reports
Extortion