Expert Services
Take it to the Next Level
with Expert Support
Get more impact out of threat intelligence
Identify possible weaknesses with our specialized services and interaction with threat actors. Get extensive and thorough threat reports with analysts that are assigned to threats based on their comprehensive knowledge of your industry and intimate understanding of your business needs.
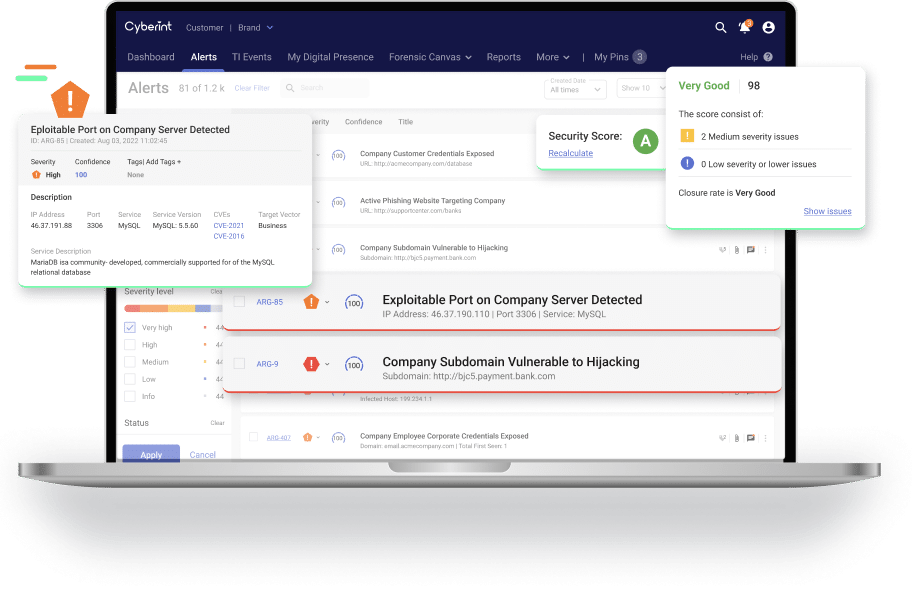
Get Holistic Coverage of Multiple Business Risk Areas
Virtual HumINT Operations
Active engagement with threat actors to learn more about their motivations, TTPs and IOCs.
Learn more 
Deep Cyber Investigations
Correlate data from a wide variety of sources to focus on gaining insights about a specific threat.
Learn more 
Threat Landscape Analysis
Get data-driven insights into threats and threat actors by building a threat actor profile.
Learn more 
Attack Simulation
Search for weaknesses and vulnerabilities in your organization’s digital surface and beyond the perimeter.
Learn more 
Fraud Takedowns and Remediation
Take down phishing sites and block threats to defend against and mitigate future attacks.
Learn more 
Third-Party Cyber Risk
Identify and measure the cyber security risk within your supply chain according to severity of the risk.
Learn more