DEEP & DARK WEB
Infiltrate the deepest, darkest corners of the underground
Cyberint helps access top-tier sources in the dark web. We collect and analyze data from elusive web sources that most other companies cannot penetrate. We enrich our automated collection with a human approach, through research and analysis of our expert team.
Understand and engage with the dark side
Cybercriminals lurk in the dark web where they can methodically coordinate their attacks, distribute malware and phishing kits, sell illicit goods, and share other pre-built exploits. But accessing the information your organization needs from the dark web can be inefficient, time consuming, and risky. In addition, many high-value closed sources present technical and financial barriers to entry.
Using technology with a human touch, however, Cyberint can access the most restricted channels to engage with threat actors and anticipate attacks targeting your organization, employees, and customers.
Uncover your compromised credentials from the deep and dark web.
Fill in your business email to start.
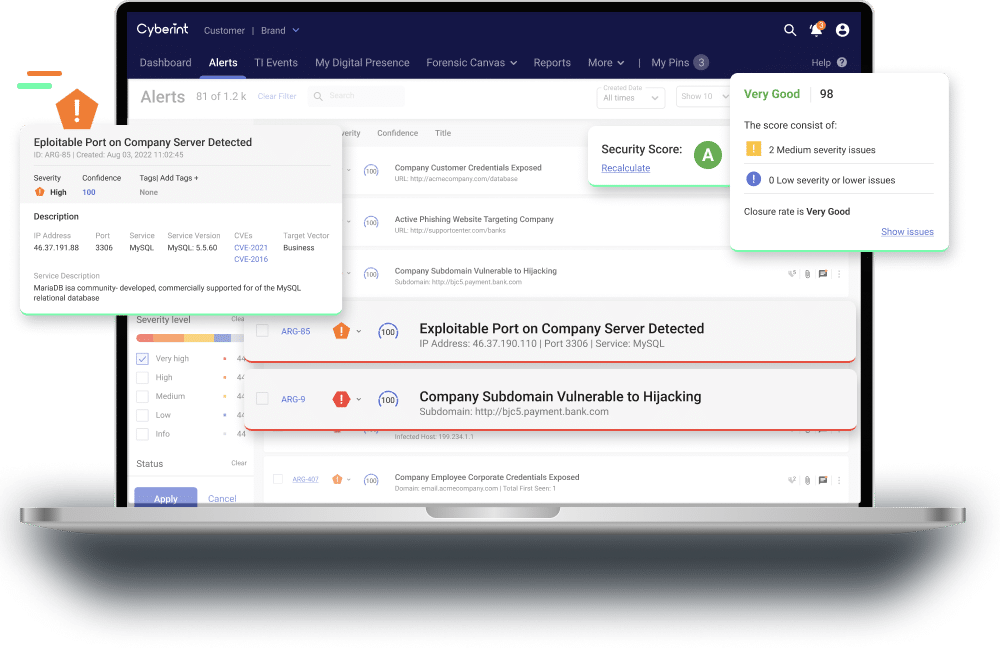
Why Customers Choose Argos Edge™
Gain targeted intelligence in real time
from thousands of sources in the open, deep, and dark web, in addition to operational threat intelligence from different feeds.
Combine an AI and human approach

Cut through the noise

Expand your visibility into the Dark web

Testimonials
Dive into our Resources
Focused intelligence.
Groundbreaking efficiency.
Real-time threat intelligence, tailored to your attack surface