On December 19, 2023, the FBI successfully dismantled one of the ALPHV/BlackCat ransomware sites. The customary FBI banner now adorns its main page, while the other sites associated with the cybercrime gang remain operational. This development may be linked to the recent 5-day disruption of the entire gang’s Darknet infrastructure.
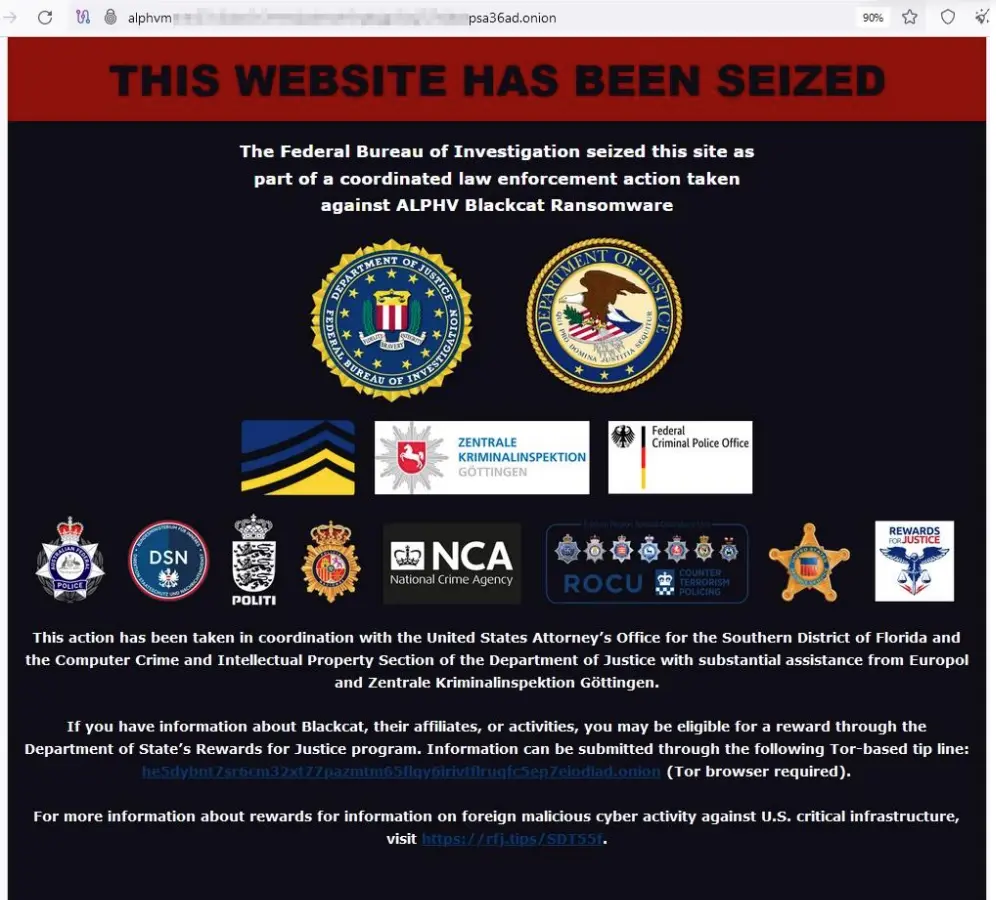
Rumors of a law enforcement operation causing an outage affecting ALPHV ransomware gang’s websites circulated on December 8, later proven true. The ALPHV (aka BlackCat) negotiation and data leak sites abruptly became unavailable, and this downtime persisted for 30 hours. When questioned about the disruption, the Admin for ALPHV assured BleepingComputer that the sites might be back online soon, which did not materialize.
In a press conference on December 19, the Justice Department announced a disruption campaign against the BlackCat ransomware group, also known as ALPHV or Noberus. This group had targeted the computer networks of over 1,000 victims worldwide, causing significant harm, including networks supporting U.S. critical infrastructure.
The FBI developed a decryption tool enabling FBI field offices across the country and global law enforcement partners to offer more than 500 affected victims the capability to restore their systems. The network infrastructure takedown represents a new trend led by the FBI, following previous actions such as QakBot infrastructure ruination, IPStorm botnet disruption, and Trigona ransomware servers wiping. The seizure of ALPHV sites adds to this list.
While the FBI’s action has disrupted ALPHV, it is unlikely to entirely halt the ransomware gang. Large players like ALPHV have the financial resources to endure an idle period. Ransomware groups that face shutdown often re-emerge as entirely new entities or collaborate with existing groups. For instance, former members of GandCrab formed REvil in 2019, even after key members were arrested in January 2022 in Russia.
Affiliates in these groups often exhibit little loyalty to a specific entity, providing Ransomware-as-a Service to multiple groups for a fee. This means that even after a major gang is arrested or shut down, affiliates continue to operate. The future of ransomware gangs is likely to follow a similar pattern, with the most successful groups dominating attacks in terms of volume and fees. While focusing on arrests is crucial, organizations should proactively enhance their security measures to mitigate risks and vulnerabilities.
There are indications that ALPHV are operating out of a different domain already.
To learn more about how our threat intelligence research helps protect businesses against ransomware and other risks, request a demo.
Fill in your business email to start.
Fill in your business email to start