Highly motivated, problem solver, dot connector, energetic multi-dimensional & professional management with commercially oriented, customer service skills & PMO abilities in high-growth, fast-paced organizations.
As we witness history in the making, the scale and complexity of the conflict are immeasurable.
When focusing on the cyber warfare aspect of the conflict we can see, first time in history, warfare that includes every type of cyber-personal, state-sponsored groups, ransomware groups, hacktivists, DDoS actors, script kitties and even volunteers that want to join the cause.
This event is one of the most significant in this century, given the fact that any civilian in the world can take place in this conflict, with a browser and computing power and we see those effects taking place, from websites that break down to multiple data leakage events.
Since the moment Russia has made the first move, infiltrating into Ukraine, we have witnessed massive attacks against several Ukraine entities. While the first 48 hours comprised of mainly Russian attacks, Ukraine-associated entities and other supporters around the world do their best to compromise and takedown Russian targets as well.
One of the first attacks initiated against Ukraine was a distributed denial-of-servers (DDoS) attack that lead to Ukraine’s Defense Ministry, PrivateBank and Oschadbank websites being out of service for several hours. Given the fact that Russia is well funded with resources to initiate such an attack, these targets’ odds to stand against this attack are very slim.
In addition to Russia’s efforts to compromise financial and government entities with DDoS attacks, security researchers at ESET, Symantec, and SentinelOne had discovered a costume-made wiper malware, HermeticWiper, that is targeting Ukrainian organizations, spreading itself and wiping Windows machines.
Up until now, no group has been linked to HermeticWiper, although given the cases we have seen of Russian campaigns such as WhisperGate in January, and the fact that this wiper utilizes techniques that were used by APT33 and Lazarus group, we can conclude the skill and capabilities that the group that created this wiper has.
The wiper is mainly targeting Ukraine, but it was also witnessed in neighboring countries and allies.
One of the more common speculations around Russia’s cyber-warfare against Ukraine is the recruitment of APTs. This is not the first time we see a relationship between certain APTs to the Russian government and Russia’s interests.
SandWorm might be the biggest threat group that publicly gets involved in this campaign. SandWorm, aka Unit 74455, is one of Russia’s state-sponsored groups that are in charge of major espionage and hacking campaigns against Ukraine for years. the most famous campaign against Ukraine is the NotPetya, while they are also responsible for the Ukraine power grid cyberattack, French presidential election, 2018 Winter Olympics, and targeting several VIP personnel in the US. The group has been active for at least 8 years.
Although Russia has started this campaign very strongly, causing severe damage to many Ukrainian infrastructures, Ukraine was able to leverage international empathy and their best efforts to cause the same, if not more damage, to Russia in return.
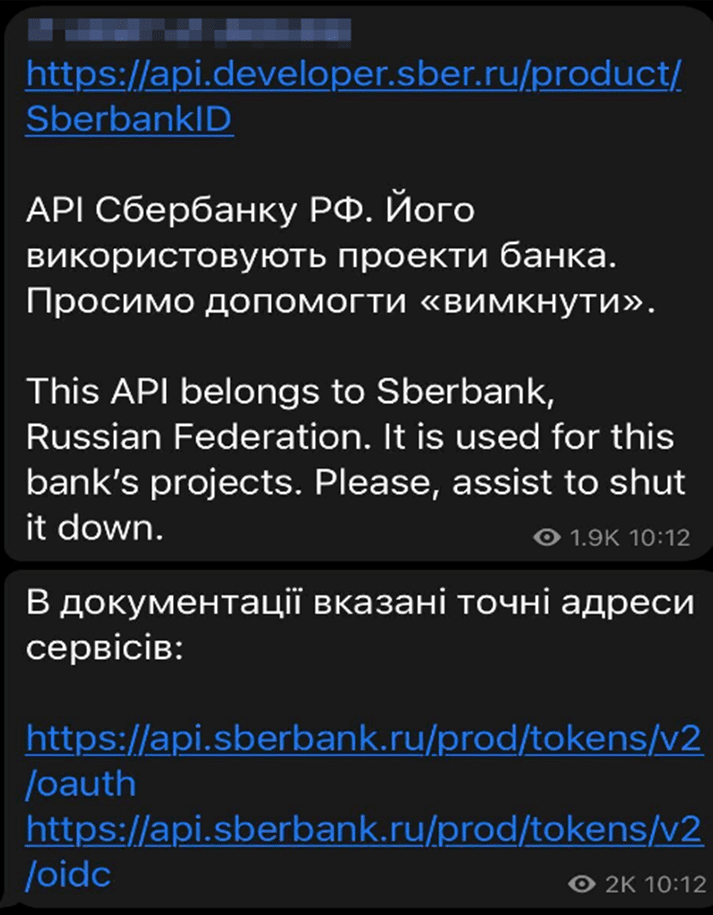
As the combat technique in the Ukrainian military has turned into somewhat of guerrilla warfare, it seems that In the cyber realm it is not that different. Many Ukrainian entities opened Telegram channels whose purpose is to recruit people from around the world that are willing to fight for Ukraine and take part in its’ cyber warfare efforts.
The nature of these groups is encouraging their members to perform DDoS attacks on Russian targets by command while the admins offer guidance and tools to do so (Figure 1).
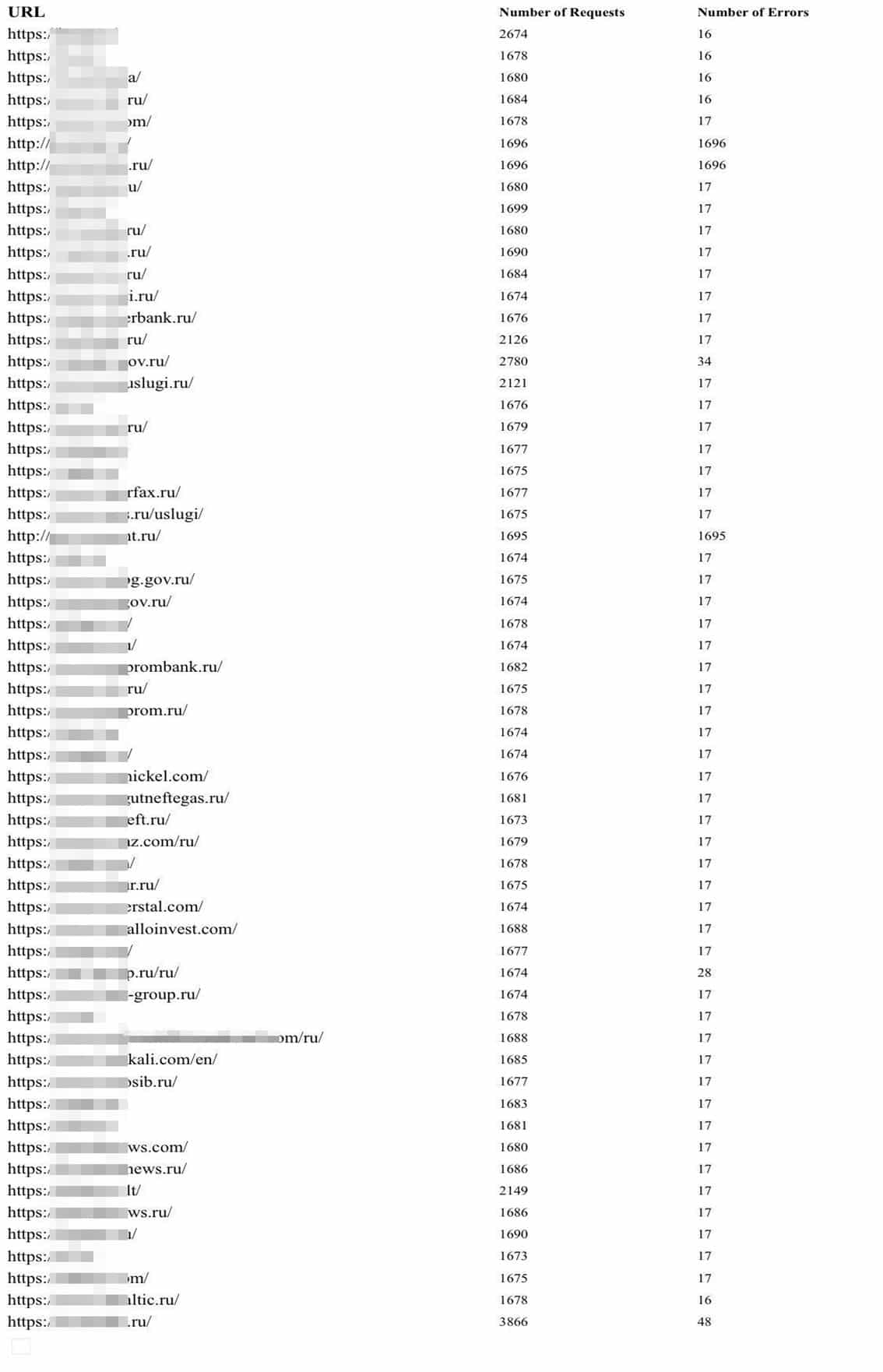
Furthermore, several websites were created in order to initiate and monitor DDoS attacks that are being deployed against Russian institutes at any given moment (Figure 2).
Fill in your business email to start