Monster, a novel Ransomware-as-a-Service (RaaS) built on Delphi, surfaced in March 2022 and caught the attention of the BlackBerry Incident Response (IR) team during an incident investigation. After its initial appearance, Monster’s capabilities and its ransomware partnership program were promoted on the Russian Anonymous Marketplace (RAMP) in June.
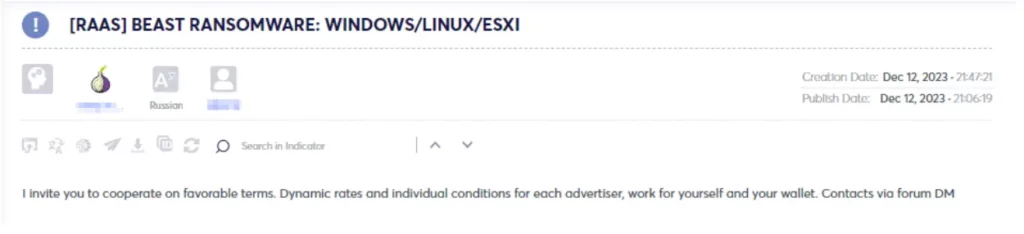
The mastermind behind Monster ransomware later introduced an enhanced version named Beast Ransomware, incorporating advanced features. Unlike its predecessor, Beast Ransomware extends its reach beyond Windows systems, targeting Linux and ESXI operating systems as well.
Similar to several ransomware strains originating or advertised in Eastern Europe, Monster avoids encrypting data on devices in specific countries. It identifies a machine’s country code through the GetLocaleW function, exempting 12 Commonwealth of Independent States (CIS) countries, including Armenia, Azerbaijan, Belarus, Georgia, Kazakhstan, Kyrgyzstan, Moldova, Russian Federation, Tajikistan, Turkmenistan, Ukraine, and Uzbekistan. Outside these countries, the ransomware operator retains the ability to target any entity or location of their choice.

Aside from assessing the victim’s machine country code, Monster enables attackers to monitor target IP addresses and locations through the IP Logger web service. Delivered as a 32-bit binary, Monster features a concealed user interface granting threat actors control over various aspects, such as selective encryption, self-deletion, and manipulation of services and processes. The ransomware is highly adaptable, allowing threat actors to define custom extensions and craft personalized ransom notes.
The subsequent iteration, Beast Ransomware, introduces several enhancements:
The modus operandi suggests that the operators likely originate from the Eastern European or Russian side of the globe.
Although Monster was around for a while, the operators still weren’t able to position Monster as a leading RaaS for threat actors to use. While they hope the Beast will do the trick, it is still considered an early-stage RaaS that doesn’t have a massive impact in the wild yet.
Cyberint, the Impactful Intelligence company, reduces risk by helping organizations detect and mitigate external cyber threats before they have an adverse impact. The Cyberint Argos platform’s patented technology provides superior visibility through continuous discovery of the evolving attack surface, combined with the automated collection and analysis of vast quantities of intelligence from across the open, deep and dark web. A team of global military-grade cybersecurity experts work alongside customers to rapidly detect, investigate, and disrupt relevant threats – before they have the chance to develop into major incidents.
Global customers, including Fortune 500 leaders across all major market verticals, rely on Cyberint to protect themselves from an array of external risks, including vulnerabilities, misconfigurations, phishing, impersonation attacks, malware infections, exposed credentials, data leaks, fraud, and 3rd party risks.
Fill in your business email to start.
Fill in your business email to start