


Threat intelligence solutions provide security teams with critical context on cybersecurity vulnerabilities and the threat actors seeking to exploit them. This helps organizations to respond proactively and efficiently to threats.
Yet while all threat intelligence tools offer the core feature of basic information about cybersecurity threats, they vary significantly in the ways they make available that data. They also differ widely in the extent to which they help security teams make actionable use of threat intelligence insights, and in their ability to keep pace with the constantly changing threat landscape.
With that reality in mind, here’s a primer on what to look for when selecting a solution within the fast-evolving cybersecurity threat intelligence landscape. This article identifies sixteen key features that a comprehensive threat intelligence tool should provide. How does yours compare?
At any moment, a business may face hundreds or even thousands of potential threats. What’s more, those threats change constantly, and new ones appear all the time.
Given this scale, threat intelligence tools must deliver threat data and help teams make use of it in an automated way. They should include malware analysis tools to help identify relevant threats automatically. Threat feeds are also critical, so that new threat data is easy for stakeholders to access. Finally, automated patch prioritization recommendations help engineers determine which threats pose the greatest risk.
Not all threats affect all organizations in the same way. To deliver the greatest value, threat intelligence solutions should be customizable in such a way that they can focus on the categories of threats that are most relevant to a particular organization. This is based on factors such as the types of workloads the organization uses, how its IT environments are built (using the cloud or on-prem infrastructure, for instance) and industry-specific compliance rules.
Learn why your brand protection relies on threat intelligence here >>
As the European Union Agency for Cybersecurity notes, a key challenge in threat intelligence is achieving the ability “to digest, consolidate and disseminate existing practices”. This ability helps teams make actionable use of threat intelligence data.
That’s why threat intelligence must be easy for humans to interpret. Tools should make clear what the nature of each threat is, its level of severity and which specific systems it affects.
Equally important is providing actionable guidance in the form of incident response plans that teams can use to remediate the threat. When threat intelligence tools tell you not just what the risk is but also how to address it, you get the fastest, most efficient remediation.
“Security data visualization is becoming extremely important due to big data, machine learning and exploratory data analytics,” according to Balaji Balakrishnan of the SANS Institute.
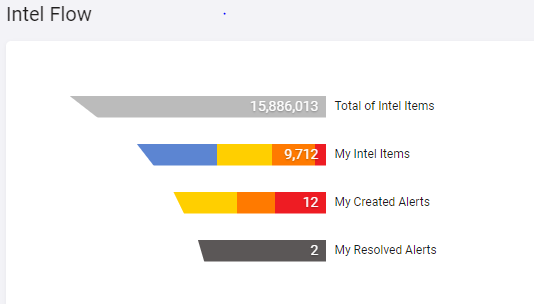
Cybersecurity threat intelligence tools should offer visualizations that help engineers understand relevant trends within threat data, assess the severity of different threats and so on. Delivering threat data in text form is not always enough to ensure that teams can use the data meaningfully.
Given that the core goal of threat intelligence is to help teams respond proactively to vulnerabilities before their environments are breached, it’s critical to gather data about threats in real-time. Historical threat intelligence data is useful as well, but real-time context and alerts are essential for achieving the main goal of threat intelligence.
The security team doesn’t only need to know which threats exist. It also needs insight into who is behind those threats and what their motives are. There is a big difference between a script kiddie whose goal is to exploit vulnerabilities just for the thrill and nation-state attackers pursuing a cyberespionage agenda, for instance. Your threat intelligence solution should help you know who your potential attackers are and what they are seeking.
Along similar lines, you need to know where threats originated, how they have evolved over time and what is likely to happen next. Threat intelligence reports should deliver this complete context, rather than merely telling you about the state of a threat at a given point in time.
See how threat intelligence could have prevented major attacks >>
Although the security team is the primary stakeholder in threat intelligence, it’s often necessary to share information about threats and response plans with other stakeholders, like developers and business managers. Threat intelligence solutions that offer built-in reporting tools make this easy to do.
The cybersecurity threat intelligence lifecycle doesn’t end with threat remediation. The final step is using feedback from the process to determine which changes the team should make, if any, to harden its defenses going forward. Here again, threat intelligence tools that generate reports about threat origins, severity level and remediation steps allow teams to incorporate feedback into the threat intelligence process.
Avatars are used by cybersecurity teams under an alias on the dark web. They deceive threat actors into giving away crucial information in order to thwart the threat actor and protect their customers. Best in class threat intelligence tools utilize this method to best protect their customers. They MUST have the ability to interact with threat actors. This is one of the benefits of a threat intelligence solution involving real live humans (Virtual HumINT) as opposed to just AI on its own.
Cybersecurity threat intelligence is only one part of a modern cybersecurity toolset. It should not be siloed from other types of tools that play a critical role in security operations, like SIEM and SOAR platforms. Threat intelligence solutions and the data they generate should integrate automatically with other platforms.
In complex scenarios, it’s difficult to determine manually how different types of threats and threat actors relate to each other. Forensic canvas features solve this problem by automatically correlating and enriching threat intelligence data to provide holistic context into security risks.
When possible, cybersecurity threat intelligence tools should minimize the time it takes to remediate a risk by taking it down automatically, without waiting on human engineers to intervene.
Although the main goal of threat intelligence tools is to provide concise, readily actionable threat intelligence, teams may sometimes need to dig deeper into the raw data behind threat intelligence alerts. Solutions should allow end-users to do this so that they can gain as much context as they need.
To make the most of threat intelligence, teams must know both how severe a threat is, and how confident threat intelligence analysts are in their assessment of a threat. Solutions should expose both types of insights.
You could sum up the features described above by saying that threat intelligence tools must be truly intelligent in order to deliver fully on their promise. In other words, they must provide customized, actionable insights and recommendations that help teams remediate threats before an active attack begins. That’s the crucial difference between threat intelligence solutions that simply tell you that a threat exists, and those that help you understand and defend against it.
To find out more about Cyberint’s Threat Intelligence services get in touch here.
Fill in your business email to start


