- Table of contents
The author
Naftali Goodman
Self-Published Author and a digital marketing specialist. Read his thought leadership articles for information on the Attack Surface and Threat Intelligence.
Table of contents
#OpIsrael Campaign 2022
IT’S THAT TIME OF THE YEAR: APRIL 7TH WILL MARK THE ANNUAL CYBER THREAT CAMPAIGN TARGETING ISRAELI ORGANIZATIONS
Introduction
OpIsrael campaigns started way back in 2013 when Anonymous, the hacktivist cyber organization, launched a coordinated cyber-attack against Israeli websites. The attack dealt no actual damage but since then, every year around April 7th, Threat Actors try to attack various Israeli websites. In the 2019 campaign, over 120 websites were breached by various Threat Actors. The hackers installed a hidden backdoor on the servers that allowed them to erase the site, vandalize it and even use it to infect other users. OpIsrael is a great opportunity for organizations with a political agenda to try and attack Israel in cyberspace. The list of websites attacked includes municipal websites, private organizations, and more.
In this report, we highlight the main threats and findings of our monitoring of the most influential organizations and groups, that might partake in activity against Israel in the upcoming OpIsrael campaign and maps their potential targets and TTPs. The findings are based on monitoring Argos™ platform and several social media accounts and pages of anti-Israeli hacktivists known for participating in former OpIsrael campaigns.
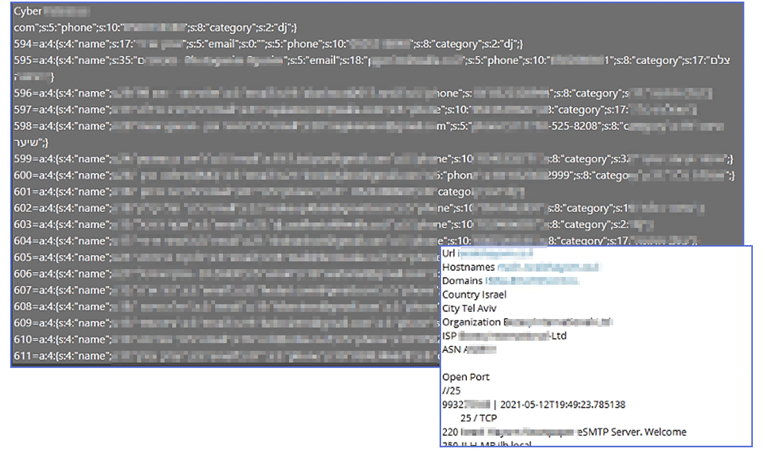
While most of the posts and tweets are only for intimidating and threatening purposes, others were included actionable Israeli IOCs (domains, exploitable IPs, leaked credentials) to encourage others to attack Israel in the upcoming OpIsrael event.
Furthermore, notably, all groups are currently conducting an ‘OP’ campaign not only against Israel, but also against several “aggressive” countries (from their point of view) currently in the midst of military conflicts. The main countries are Israel, Russia, India and Indonesia.
Cyberint found that an influx in the activity against Israel on social media occurred at the beginning of December 2021 when hacktivists began warning Israel about the upcoming OpIsrael campaign, in addition to several Israeli companies from the private sector that had already been hacked.
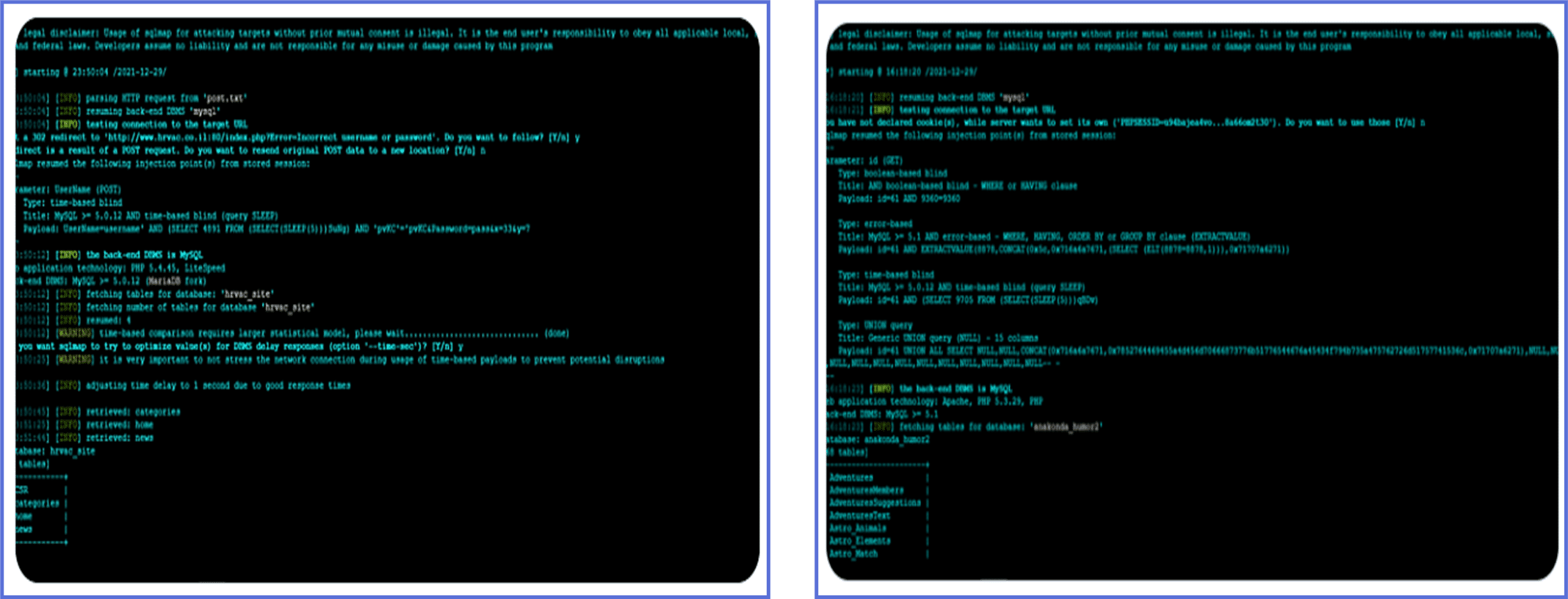
Lastly, Cyberint recommends reinforcing the security network infrastructure against DDoS attacks and SQL injections as those are the types of attacks that were recognized as commonly used by the hacktivist groups of the OpIsrael Campaign.
Main ‘OpIsrael’ Active Groups
Cyberint identified the main hacktivists groups traditionally participating in the OpIsrael campaigns. Most groups have several branches or sub-groups based on geographic location mainly in Israel, India, Malaysia, Singapore, and, Indonesia. All groups are collaborating and managed by hacktivists but the professionality of the members and their sophistication differs significantly between the different groups.
Some groups seem to be more advanced and sophisticated than others. They often publish very detailed information such as a list of potential targets and give recognition to the Threat Actors over successful cyber attacks in addition to tools for conducting attacks. One of these groups took responsibility for attacking more than 200 Israeli Websites.
Other groups publish mainly political propaganda posts, threat videos, slogans and hashtags to later be used on social media campaigns. Both types of activity can be seen in all groups and aimed to encourage others to attack Israeli websites by providing propaganda alongside multiple lists of domains and exploitable IPs.
Recommendations
- Cyberint will keep monitoring the mentioned groups throughout the campaign period to identify any activity or additional IOCs that could indicate which are the potential targets in this campaign.
- As DDoS attacks are a very common technique used by hacktivist groups, is it advised to prepare the security network infrastructure for this type of attack by ensuring the following tools and procedures are set up accurately:
- Load balancer server that will ensure you do not have any network bottlenecks or single points of failure.
- Firewall and intrusion detection systems that are able to act as traffic-scanning barriers between networks.
- Backup servers infrastructure and DDoS response plan in case of a successful DDoS attack.
- As SQL injection was used lately by Anonimous group in OpRussia campaign, it is advised to prepare the security network infrastructure for this type of attack by ensuring the following tools and procedures are set up accurately:
- Utilizing parameterized database queries with bound, typed parameters and careful use of parameterized stored procedures in the database.
- Firewall, WAF, and intrusion detection systems to be able to block any suspicious activity.
- Endpoint security that ensures network endpoints do not become an entry point for malicious activity.
- Segregate SQL servers containing sensitive information from SQL servers that are front-facing and receive data from users as much as possible.
Appendix
Israeli websites that might be targeted, Government, banks and E-commerce:
| www.idf.gov.il www.idf.il www.ifts.gov.il www.iibr.gov.il www.iiop.gov.il www.immigration.gov.il www.ims.gov.il www.index.gov.il www.info.gov.il www.int.gov.il www.ips.gov.il www.shabas.gov.il www.isa.gov.il www.israbank.gov.il www.israc.gov.il www.israel.gov.il www.trade.gov.il www.visitisrael.gov.il www.water.gov.il www.zchut.gov.il goldface.hug.co.il arens.co.il iforc.co.il itailewin.com comtop.co.il arditi.co.il eid-store.co.il moranwine.co.il www.vidoflex.com mecad.co.il www.omega-audio.co.il www.achbooks.co.il www.microgil.com www.neo-humanology.org.il www.meiri-tec.co.il www.rgdesign.co.il www.mizugim.co.il www.i-factor.co.il rafael-law.co.il taijichen.quickyweb.biz melech-al-hayav.co.il www.pollakmaps.com ultimate.hug.co.il www.shacharut.org.il www.tikshoretnet.co.il www.medicheck.org mendi.co.il vardawigs.co.il www.bbhi-il.com www.arditi.co.il www.tre-israel.com www.vidoflex.com www.zichronyaacov.co.il www.vidoflex.com www.smartpage.az-ma.co.il www.shacharut.org.il www.smartspace.co.il www.habait.co.il www.rgdesign.co.il www.zichronyaacov.co.il xcamp.hug.co.il z-n-gur.com www.kathynuriel.co.il www.mizugim.co.il www.eft4life.co.il www.az-ma.co.il www.hadaralon.co.il center-computers.co.il eid-store.co.il moranwine.co.il www.vidoflex.com mecad.co.il www.omega-audio.co.il www.achbooks.co.il www.microgil.com www.arens.co.il www.pollakmaps.com www.at-lan.co.il tevakat.co.il www.derech-tipul.co.il www.smartpage.az-ma.co.il www.avishushan.co.il palmach-mh.co.il www.tobeima.co.il www.funkybeat.hug.co.il www.horashim.co.il www.remaxmodiin.co.il www.iforc.co.il www.2go2.co.il www.gardeners4gardens.co.il www.improco.co.il www.melech-al-hayav.co.il www.eft4life.co.il familyconstellations.co.il www.microgil.com www.mizugim.co.il www.tobeima.co.il www.imt.co.il www.rgdesign.co.il www.smartspace.co.il www.habait.co.il www.rgdesign.co.il www.zichronyaacov.co.il xcamp.hug.co.il www.aa.gov.il www.agri.gov.il www.antidrugs.gov.il www.antitrust.gov.il www.archives.gov.il www.ashra.gov.il www.auco.justice.gov.il www.bankisrael.gov.il www.boi.gov.il www.btl.gov.il www.bus.gov.il www.caa.gov.il www.cbs.gov.il www.cert.gov.il www.civil-service.gov.il www.court.gov.il www.dat.gov.il www.defence.gov.il www.dev.cbs.gov.il www.eca.gov.il www.ecom.gov.il www.ecom1.gov.il www.edu.gov.il www.edu-negev.gov.il www.moag.gov.il www.moc.gov.il www.moch.gov.il www.mod.gov.il www.mof.gov.il www.mofa.gov.il www.mohr.gov.il www.moia.gov.il www.moin.gov.il www.moit.gov.il www.moital.gov.il www.molsa.gov.il www.mops.gov.il www.mossad.gov.il www.most.gov.il www.mot.gov.il www.mrc.gov.il www.msh.gov.il www.nativ.gov.il |
www.israel-info.gov.il www.israel-mfa.gov.il www.israeltrade.gov.il www.itpolicy.gov.il www.jda.gov.il www.jtmt.gov.il www.justice.gov.il www.kids.gov.il www.knesset.gov.il www.kranoth.gov.il www.laad.btl.gov.il www.ladpc.gov.il www.lapam.gov.il www.m-adumim.gov.il www.magna.isa.gov.il www.maor.gov.il mag.az-ma.co.il eddigraf.com www.pollakmaps.com www.bbhi-il.com alevi.co.il avishushan.co.il coffie-mechine.co.il smartspace.co.il www.coffie-mechine.co.il www.stickler.co.il terra-stone.co.il www.arens.co.il www.pollakmaps.com www.at-lan.co.il tevakat.co.il www.derech-tipul.co.il www.smartpage.az-ma.co.il www.avishushan.co.il palmach-mh.co.il www.tobeima.co.il www.funkybeat.hug.co.il www.horashim.co.il www.remaxmodiin.co.il www.iforc.co.il www.2go2.co.il www.gardeners4gardens.co.il www.improco.co.il www.melech-al-hayav.co.il www.eft4life.co.il www.stylebed.co.il www.icu.az-ma.co.il www.mecad.co.il www.itailewin.com www.2go2.co.il www.morcook.co.il www.achbooks.co.il www.orit-guez.co.il www.rgdesign.co.il www.stylebed.co.il www.rafael-law.co.il www.tikshoretnet.co.il www.palmach-mh.co.il www.neo-humanology.org.il www.meiri-tec.co.il www.rgdesign.co.il www.mizugim.co.il www.i-factor.co.il rafael-law.co.il taijichen.quickyweb.biz melech-al-hayav.co.il www.pollakmaps.com ultimate.hug.co.il www.shacharut.org.il www.dalia-mosaic.co.il www.neo-humanology.org.il www.migueltomer.hoogel.co.il www.kathynuriel.co.il www.mizugim.co.il www.stylebed.co.il www.icu.az-ma.co.il www.mecad.co.il www.itailewin.com www.2go2.co.il www.morcook.co.il www.achbooks.co.il www.orit-guez.co.il www.rgdesign.co.il www.stylebed.co.il www.rafael-law.co.il www.tikshoretnet.co.il www.palmach-mh.co.il www.2go2.co.il www.vardawigs.co.il www.zichronyaacov.co.il www.vidoflex.com www.smartpage.az-ma.co.il www.shacharut.org.il www.smartspace.co.il www.embassies.gov.il www.emus.gov.il www.energy.gov.il www.environment.gov.il www.eqred.gov.il www.finance.gov.il www.first.gov.il www.forms.gov.il www.galil.gov.il www.galilee.gov.il www.gca.gov.il www.gimlaim.gov.il www.gov.il www.gp.gov.il www.gpo.gov.il www.gsi.gov.il www.health.gov.il www.iaa.gov.il www.iaec.gov.il www.idf.gov.il www.idf.il www.ifts.gov.il www.iibr.gov.il www.iiop.gov.il www.immigration.gov.il www.ims.gov.il www.index.gov.il www.info.gov.il www.int.gov.il www.nazareth2000.gov.il www.negev.gov.il www.nioi.gov.il www.nisa.gov.il www.nsc.gov.il www.ocs.moital.gov.il www.oz.gov.il www.parliament.gov.il www.piba.gov.il www.pm.gov.il www.pmo.gov.il www.pnim.gov.il www.police.gov.il www.president.gov.il www.pwd.gov.il www.rbc.gov.il www.religinfoserv.gov.il www.religions.gov.il www.rsa.gov.il |
www.mapi.gov.il www.mevaker.gov.il www.mfa.gov.il www.mfah.gov.il www.misim.gov.il www.mmi.gov.il www.mni.gov.il www.moag.gov.il www.moc.gov.il www.moch.gov.il www.mod.gov.il www.mof.gov.il www.mofa.gov.il www.mohr.gov.il www.moia.gov.il www.moin.gov.il horashim.co.il www.habait.co.il alma.hug.co.il www.fortineros.com www.pollakmaps.com www.bbhi.co.il www.eft4life.co.il www.az-ma.co.il www.hadaralon.co.il center-computers.co.il www.microgil.com www.mizugim.co.il www.tobeima.co.il www.imt.co.il www.rgdesign.co.il www.dalia-mosaic.co.il www.neo-humanology.org.il www.migueltomer.hoogel.co.il www.kathynuriel.co.il www.mizugim.co.il www.stylebed.co.il www.icu.az-ma.co.il www.mecad.co.il www.itailewin.com www.2go2.co.il www.morcook.co.il www.achbooks.co.il www.orit-guez.co.il www.rgdesign.co.il www.stylebed.co.il www.rafael-law.co.il www.tikshoretnet.co.il www.palmach-mh.co.il www.2go2.co.il www.vardawigs.co.il www.2go2.co.il www.vardawigs.co.il www.zichronyaacov.co.il www.vidoflex.com www.smartpage.az-ma.co.il www.shacharut.org.il www.smartspace.co.il www.habait.co.il www.rgdesign.co.il www.zichronyaacov.co.il xcamp.hug.co.il www.tikshoretnet.co.il www.medicheck.org mendi.co.il vardawigs.co.il www.bbhi-il.com www.arditi.co.il www.tre-israel.com www.vidoflex.com smartspace.co.il www.coffie-mechine.co.il www.stickler.co.il terra-stone.co.il www.habait.co.il www.rgdesign.co.il www.zichronyaacov.co.il xcamp.hug.co.il z-n-gur.com www.kathynuriel.co.il www.mizugim.co.il www.stylebed.co.il www.icu.az-ma.co.il www.mecad.co.il www.itailewin.com www.2go2.co.il www.morcook.co.il www.achbooks.co.il www.orit-guez.co.il www.rgdesign.co.il www.stylebed.co.il www.rafael-law.co.il www.tikshoretnet.co.il www.palmach-mh.co.il www.2go2.co.il www.vardawigs.co.il www.zichronyaacov.co.il www.vidoflex.com www.smartpage.az-ma.co.il www.shacharut.org.il www.ips.gov.il www.shabas.gov.il www.isa.gov.il www.israbank.gov.il www.israc.gov.il www.israel.gov.il www.israel-info.gov.il www.israel-mfa.gov.il www.israeltrade.gov.il www.itpolicy.gov.il www.jda.gov.il www.jtmt.gov.il www.justice.gov.il www.kids.gov.il www.knesset.gov.il www.kranoth.gov.il www.laad.btl.gov.il www.ladpc.gov.il www.lapam.gov.il www.m-adumim.gov.il www.magna.isa.gov.il www.maor.gov.il www.mapi.gov.il www.mevaker.gov.il www.mfa.gov.il www.mfah.gov.il www.misim.gov.il www.mmi.gov.il www.mni.gov.il www.sep.gov.il www.shaam.gov.il www.shabak.gov.il www.shaham.moag.gov.il www.soi.gov.il www.soreq.gov.il www.spring.gov.il www.sra.gov.il www.sviva.gov.il www.taasuka.gov.il www.tamas.gov.il www.tayman-child.gov.il www.tehila.gov.il www.tel-aviv.gov.il www.tipa.gov.il www.tofes.gov.il www.tourism.gov.il |